The core mission within the (NOC) is community resilience. We additionally present built-in safety, visibility and automation: a SOC (Safety Operations Heart) contained in the NOC, with Gifter and Bart because the leaders.

Partially one, , we coated the community:
- Designing the Black Hat Community
- AP (Entry Factors) Placement Planning, by Uros Mihajlovic
- Safety Heart Investigations, by Uros Mihajlovic
- Meraki and ThousandEyes, by Uros Mihajlovic
- Meraki Dashboards, by Steven Fan
- Meraki Alerting, by Connor Loughlin
- Meraki Techniques Supervisor, by Paul Fidler
- A Higher Technique to Design Coaching SSIDs/VLANs, by Paul Fidler
Partially two, we deal with safety:
- Integration is Key to Safety
- Integrating Safe Cloud Analytics into the Black Hat Ecosystem Story, by Ryan MacLennan
- What’s Your VPN (Digital Non-public Community) Doing within the Background, by Aditya Raghavan
- Script Kiddie will get a Timeout, by Ben Greenbaum and Shawn Coulter
- Correlating Meraki Scanning Knowledge with Umbrella DNS (Area Identify Service) Safety Occasions, by Christen Clauson
- Area Identify Service Statistics and Improved Visibility, by Alejo Calaoagan
Integration is Key to Safety
For Black Hat Asia 2023, Cisco Safe was the official Cell Gadget Administration, DNS and Malware Evaluation Supplier.
Because the wants of Black Hat developed, so did the Cisco Safe Applied sciences within the NOC:
The Cisco XDR dashboard made it simple to see the standing of every of the linked Cisco Safe applied sciences, and the Meraki APs for the community.
Since becoming a member of the Black Hat NOC in 2016, I frequently advocate for integration and automation. Black Hat 2023 was essentially the most built-in NOC so far.

This requires collaboration and open communication with the NOC companions.

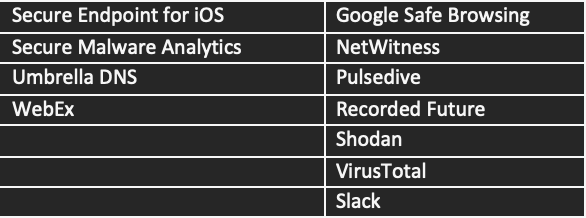
Under are the Cisco XDR integrations for Black Hat Asia, empowering analysts to research Indicators of Compromise (IOC) in a short time, with one search.

The integrations comprised two screens. So as to add an integration, we merely click on on the module within the checklist beneath after which add the API (Software Programming Interfaces) key.

We recognize , and donating full licenses to the Black Hat Asia 2023 NOC.

File Evaluation and Teamwork within the NOC
Corelight and NetWitness extracted a number of PDFs from the convention community stream, which had been despatched for evaluation in Cisco Safe Malware Analytics (Menace Grid). Within the glovebox video, they had been noticed as quotes from an Audio-Visible rental firm vendor working on the Black Hat convention. The quotes contained private and proprietary enterprise data, which might make it fairly simple to craft spear phishing assaults in opposition to each the rental firm and the shoppers.

Investigation by the Corelight staff decided the person downloaded the primary file through HTTP from an unsecure portal [http://imxx[.]netxxx.com[.]sg/login/login[.]cfm], with login credentials within the clear.

Then they emailed through unsecure SMTP protocol to the consumer. The Palo Alto Firewall staff confirmed the SMTP e mail and recordsdata.

The NetWitness staff reconstructed the emails. The NOC staff created a findings report for the seller, to assist them in securing their webserver and switching to a safe e mail protocol.

Integrating Safe Cloud Analytics into the Black Hat Ecosystem Story, by Ryan MacLennan
For Black Hat Asia, Cisco was in a position so as to add Safe Cloud Analytics (SCA) into the combination as a community analytics platform, to assist enrich and supply an extra layer of safety to the Black Hat convention.
To start our deployment, we first needed to deploy the brand new Cisco Telemetry Dealer (CTB); nonetheless, this will have prompted points with useful resource administration on our Intel NUC that was offering different essential infrastructure. To alleviate any useful resource administration points we might run into, we deployed a light-weight on-prem community sensor as a substitute of CTB. At future conferences, we will likely be utilizing one other NUC with CTB deployed, as that’s the really helpful technique to ship on-prem community information to SCA.

After deploying the on-prem sensor we labored with the Arista staff to get us a community faucet and enabled our Meraki MXs to ship Netflow information to the sensor.

With us getting information from Arista for something entering into or out of the community and Meraki offering NetFlow information on inner connections, we might then use the Umbrella and Meraki SCA integrations to counterpoint the community analytics inside SCA.
With these two integrations enabled we began seeing the details about every host and noticed the judgements of domains and URLs these hosts go to inside SCA.
We added personalized alerts for notification, added third get together risk intelligence lists, configured international locations we need to watch, and added teams of categorizations of our community to inform when sections of our community discuss to one another once they shouldn’t be doing so.
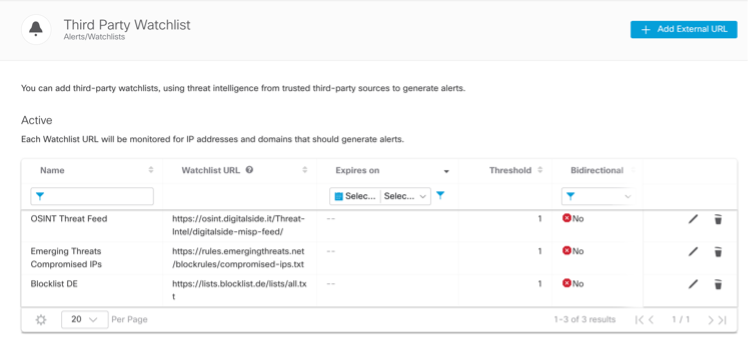
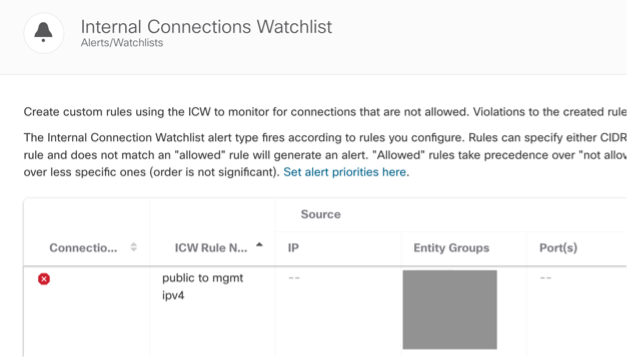

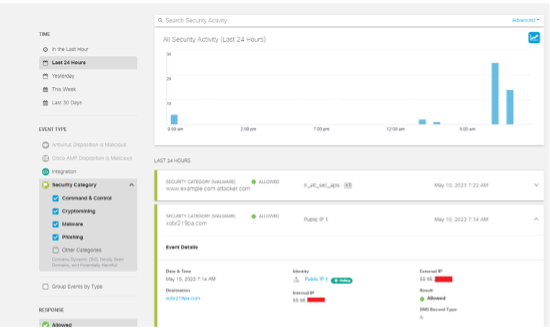
After these configurations had been put in place, we had been now capable of begin getting significant alerts about what is going on in our community. Within the picture beneath, you’ll be able to see that now we have gotten a number of alerts throughout the convention and responded to every with an investigation.

After these configurations had been put in place, we had been now capable of begin getting significant alerts about what is going on in our community. Within the picture beneath, you’ll be able to see that now we have gotten a number of alerts throughout the convention and responded to every with an investigation.
What’s your VPN Doing within the Background, by Aditya Raghavan
Safe Cloud Analytics was setup with integrations to 3rd get together watchlists, like OSINT (Open-Supply Intelligence) Menace Feed, Rising Menace Compromised IPs and Blocklist DE, along with the built-in Talos risk feed. Safe Cloud Analytics flagged a Consumer Watchlist Alert detecting uncommon site visitors to an IP on the Blocklist DE checklist, highlighting the weird site visitors dimension of simply 60 bytes to and from the watchlist IP which seemed like malware beaconing.

We dug down deeper with our companions.
The Palo Alto Networks staff confirmed this site visitors on the firewall, which helped figuring out the endpoint sourcing this site visitors. Safe Cloud Analytics additionally flagged quite a few Geographic Watchlist Observations of the identical site visitors from that endpoint to varied international locations the world over, so we noticed repeated such conduct. The Corelight staff was capable of pinpoint this site visitors to a single ICMP ping and response from the person endpoint. The hosts producing it had been flagged by Corelight as VPNInsights::PIA.



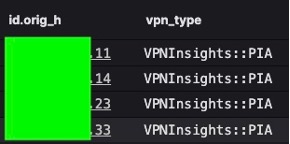
Primarily based on our evaluation, we had been capable of pinpoint this site visitors being produced by Non-public Web Entry (PIA) VPN consumer on the person endpoint. This VPN utility was seen to ship pings to hundreds of IPs throughout all the world each 60 seconds, to check latency to the VPN headend servers.
In the long run, we discovered the underlying reason behind the bizarre site visitors that seemed like malware going to thousand IPs the world over, and decided it was nothing malicious.
Script Kiddie will get a Timeout, by Ben Greenbaum and Shaun Colter
One attendee tried to paint outdoors the traces and needed to be reminded that (via the ability of the XDR strategy, enabled by integration with a number of companions) the NOC sees all. Safe Cloud Analytics warned us, through Cisco XDR, about potential port scanning conduct emanating from the convention community in opposition to the surface world.
Inside a couple of minutes, analysts of the NOC companions had been all alerted about completely different exercise in opposition to outdoors, “actual world” targets, all from the identical host: Log4j exploitation makes an attempt, WordPress assaults in opposition to a widely known restaurant chain, SQL injection and different assaults in opposition to a outstanding cost processor, and lots of others.
The incident of Suspected Port Abuse on an Exterior goal, moved to the highest of the Incidents.
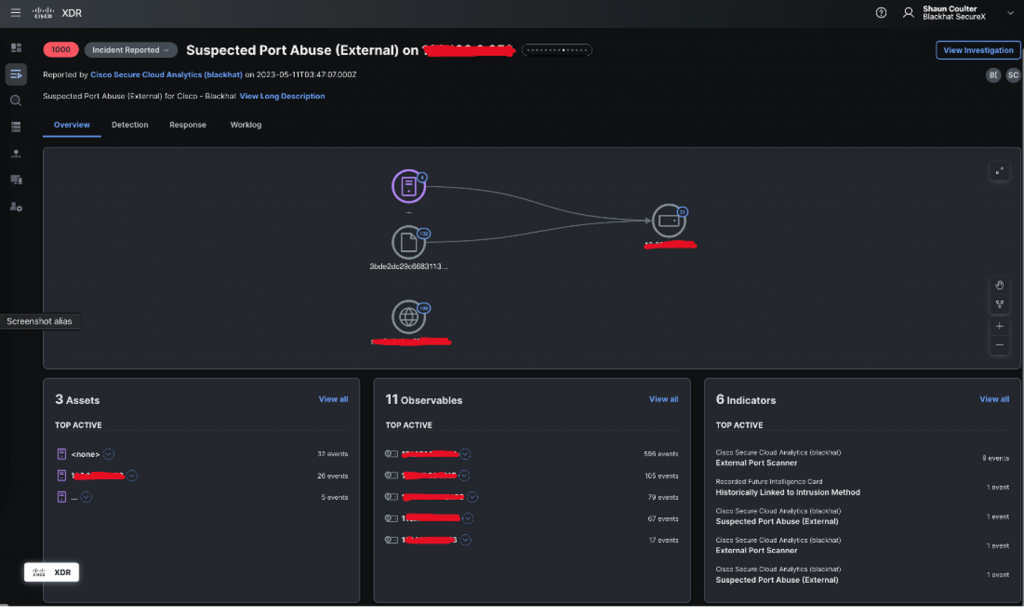
The Incident Description offered further data to collaborate with the NOC companions.

The collated occasions from all related sources are detailed within the XDR Detections web page beneath.

Community detection is a foundational pillar of safety consciousness and was the primary telemetry extensively accessible to safety operators for a cause. The supply of the scanning exercise was a tool on the final convention attendee Wi-Fi and subsequently not more likely to be related to any ongoing coaching. We investigated the gadget’s community exercise and located that the scanning comprised over 50% of their whole community site visitors at the moment. The scans focused precisely 1000 distinctive ports between 1 and 65389, and included all the standard service ports in addition to widespread secondary choices.
The NetWitness staff analyzed the PCAP (packet seize) of the assault.

The Palo Alto Networks Firewall staff alerted on a number of tried exploits.
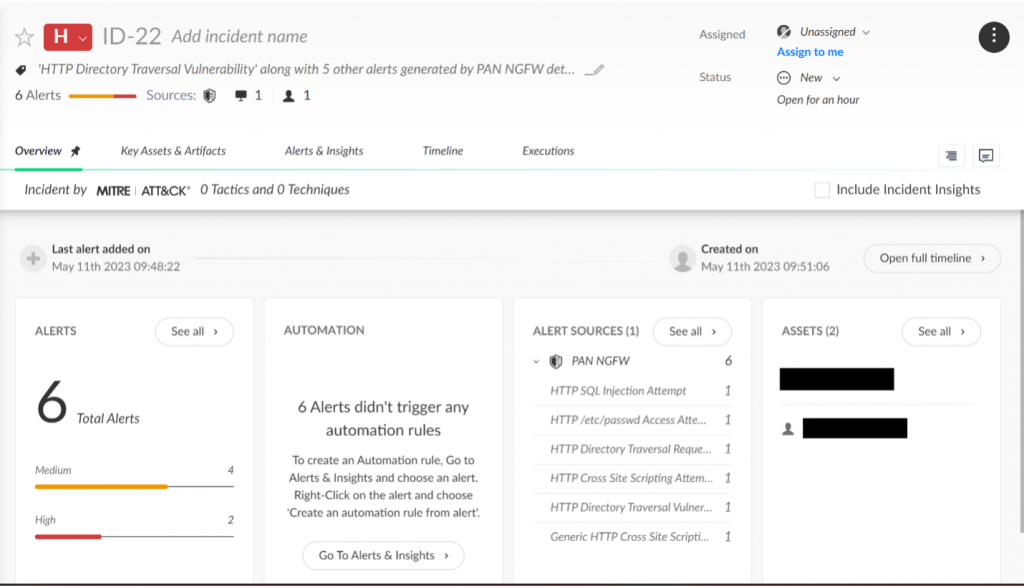
The Meraki MX Safety Workforce tracked the assaults within the Safety Heart.

The Corelight assault notices additionally confirmed the assaults.

As well as, this topic was seen performing numerous attack-adjacent actions, comparable to passive DNS analysis, CRL manipulation, HTTP scanning, port scanning and others.

The visualization in Cisco XDR helped the NOC staff perceive the scope of the assault, whereas transferring tangential data out of direct view.

Additional evaluation in these and different instruments revealed a sample of conduct that had a begin earlier within the morning, a spot of about an hour, after which roughly quarter-hour of uninterrupted excessive quantity assault exercise that signified using automation.

Whereas there are lots of issues this staff is tasked to watch however not intervene with, the Black Hat expressly forbids attacking outdoors targets from wherever throughout the Black Hat community. We offered Palo Alto Networks Firewall staff with the attacker’s MAC tackle, who initiated a captive portal for the person a captive portal that politely reminded them of the Code of Conduct and ended with “if it continues we’ll come discover you”.

It didn’t proceed.
Correlating Meraki Scanning Knowledge with Umbrella DNS Safety Occasions, by Christian Clasen
Over the past three Black Hat occasions, we used Meraki scanning information to get location information for particular person shoppers, as they roamed the convention. The venture has slowly developed from merely saving information off to flat textual content recordsdata for future evaluation, to producing heatmaps utilizing Python Folium, to populating a database, and eventually correlating Umbrella DNS safety occasions.
Because the convention grew from the pandemic-era attendance (about 20% of earlier occasions) again to full capability, we needed to make some changes to the method of ingesting the information from the Meraki streaming API. To help with different integrations, we started writing the incoming information to recordsdata as a substitute of on to the database throughout the Flask app. We then added a scheduled job to learn the recordsdata into the database each 5 seconds.
In previous conferences, we might manually run the scripts to generate heatmaps (.html recordsdata) for evaluation. This time, we needed the maps to be generated routinely, at all times be up-to-date and be accessible to everybody over an online service. So, we created a brand new module that may host one other Flask net app. Within the module, we outlined the bounds of every day in epoch time, and scheduled a job to create the maps each 5 minutes:
A map for every day was then generated and dropped into the “/templates” folder. Through the use of the “render_template()” operate, it shows the heatmap within the browser when navigating to the suitable path. For instance, we might make a request to https://webserver/wed and be served the heatmap for Wednesday, 10 Might:
This manner, anybody within the NOC might open the trail to the present day of their browser and see the most recent map as much as the earlier 5 minutes. However we didn’t need to must manually refresh the web page to get the most recent map, so we added some JavaScript that may immediate the browser to refresh. First, we added a hyperlink to “refresh.js” within the map HTML:
Then we added a easy window refresh within the file, positioned within the “templates” listing:
Area Identify Service Statistics and Improved Visibility, by Alejo Calaoagan
Since 2018, now we have been monitoring the DNS stats on the Black Hat Asia conferences. This yr’s attendance noticed effectively over 6.2 million whole DNS queries.

This was the best up to now for Black Hat Asia.

This yr’s Black Hat noticed over 1,100 apps connect with the community, practically half of what was seen final yr. This was the primary time now we have ever seen a decline within the variety of Apps.

Ought to the necessity come up, we will block any utility, comparable to any of the high-risk apps recognized above.

Bettering Community Visibility
At each Black Hat we help, we’re at all times in search of methods to enhance site visitors visibility to assist us establish malicious person exercise extra shortly. To facilitate higher information, we labored with the community design staff to outline every room and space of the convention ground with their very own VLAN and subnet.

By defining subnets and VLANs for every space in use on the present, we had been now capable of establish malicious occasions by the world the request was made. This added perception improved our information high quality and helped us establish threats and tendencies a lot quicker inside our risk looking duties.

Trying on the safety occasions above, we see that these requests got here from one of many Black Hat coaching rooms. In years previous, we must leap via a pair completely different person interfaces (Meraki/Umbrella) to validate intent and placement. Now, after a fast check-in with the coaching room teacher to verify these requests had been a part of the course curriculum, we will safely transfer on to the subsequent hunt.
Bettering visibility even additional, we labored with James Holland and the Palo Alto Networks firewall staff to assist us uncover information that’s usually masked inside Umbrella.

The savvier customers on the market could onerous code DNS on their machines to keep up some degree of management and privateness. To account for this, Palo Alto Networks NAT’ed (Community Deal with Translation) all this masked site visitors via our Umbrella digital home equipment on web site. Visitors beforehand masked was now seen and trackable throughout the VLANs and subnets outlined above. This added visibility improved the standard of our statistics, supplying information that was beforehand a black field.

That is what it seemed like contained in the Palo Alto Networks Firewall.

This allowed us to detect site visitors to a malicious area.
Then use Umbrella Examine to study extra and take applicable motion.

That may be a wrap of us, one other Black Hat Asia within the historical past books. With over 2,500 whole attendees this yr, it’s protected to say that the present was successful. Studying from previous occasions, now we have actually streamlined our deployment and investigative processes.
We’re happy with the collaboration of the Cisco staff and the NOC companions. will likely be in August 2023 on the Mandalay Bay… Hope to see you there!

Acknowledgments
Thanks to the Cisco NOC staff:
- Cisco Safe: Christian Clasen, Alex Calaoagan, Ben Greenbaum, Ryan Maclennan, Shaun Coulter and Aditya Raghavan; with digital help by Ian Redden and Adi Sankar
- Meraki Techniques Supervisor: Paul Fidler and Connor Loughlin
- Meraki Community: Steven Fan, Uros Mihajlovic and Jeffrey Chua; with digital help by Evan Basta and Jeffry Handal
Additionally, to our NOC companions: NetWitness (particularly David Glover, Iain Davidson and Alessandro Zatti), Palo Alto Networks (particularly James Holland), Corelight (particularly Dustin Lee), Arista, MyRepublic and all the Black Hat / Informa Tech employees (particularly Grifter ‘Neil Wyler,’ Bart Stump, Steve Fink, James Pope, Mike Spicer, Jess Stafford and Steve Oldenbourg).
About Black Hat
For 25 years, Black Hat has offered attendees with the very newest in data safety analysis, improvement, and tendencies. These high-profile world occasions and trainings are pushed by the wants of the safety neighborhood, striving to carry collectively the perfect minds within the business. Black Hat conjures up professionals in any respect profession ranges, encouraging development and collaboration amongst academia, world-class researchers, and leaders in the private and non-private sectors. Black Hat Briefings and Trainings are held yearly in the USA, Europe and USA. Extra data is out there at: . Black Hat is delivered to you by Informa Tech.
We’d love to listen to what you suppose. Ask a Query, Remark Under, and Keep Linked with Cisco Safe on social!
Cisco Safe Social Channels
Share:
